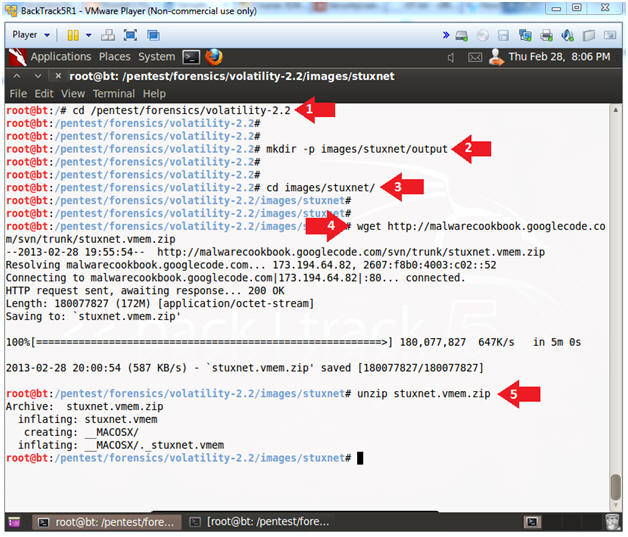
In this post I'm going to talk about Volatility. Volatility is one of the best tools for memory forensics. It is an open source framework writen in python for incident response and malware analysis.
Thanks to Malware Analyst's Cookbook we can get a real memory dump from an infected host with Zeus Trojan. You can donwload zeus.vmem.zip [41,4 MB]
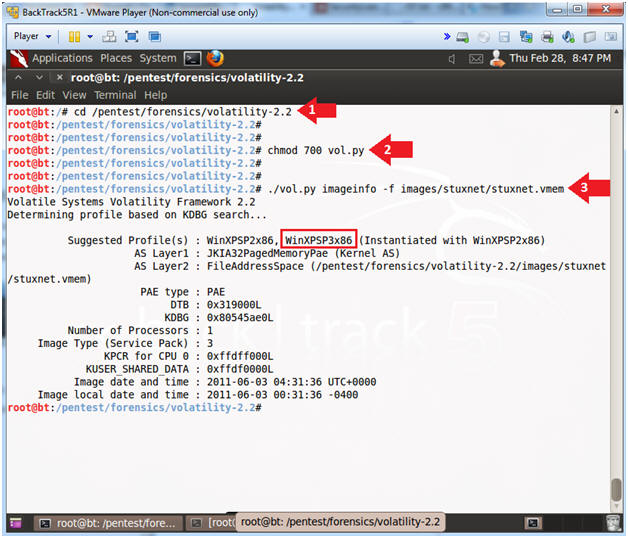
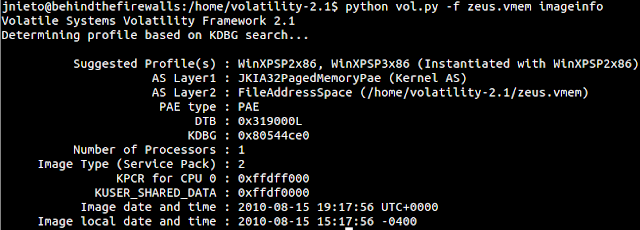
1) With the option "imageinfo" you can find out what type of OS was running.
1 | python vol.py -f zeus.vmem imageinfo |
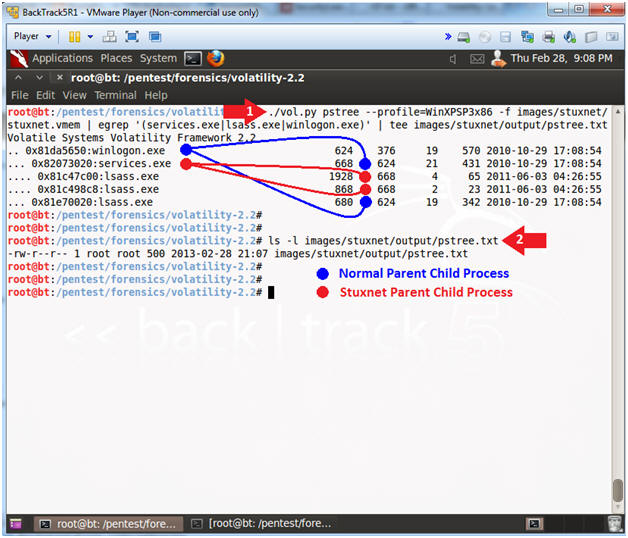
2) Now, we are going to watch what processes were running on the computer when the memory dump was recorder.
1 | python vol.py -f zeus.vmem pstree |
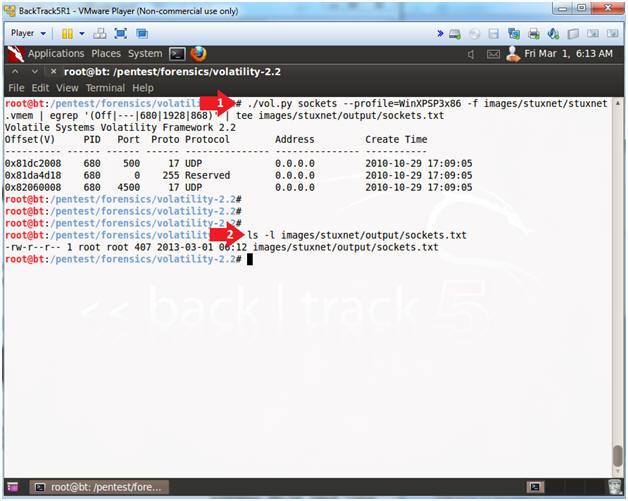
3) I couldn't see anything weird... I wanted to know if the machine was making connections...
1 | python vol.py -f zeus.vmem connscan |
4) Ok. Our machine was making connections with 193.104.47.75 by the 80/tcp port. The proccess Pid is 856. We want to know whether this process belong to an Internet Browser.
We run it again:
1 | python vol.py -f zeus.vmem pstree |
5) We can see that svchost.exe is the process which is making connections with193.104.47.75 instead of an Internet Browser... This is not common... Is this IP address blacklisted?
http://www.ipvoid.com/scan/193.104.41.75/
6) As you can see, this IP is blacklisted. It is common that a trojan adds a registry key to be sure that it will be running every time the computer is restarted. Take a look at the Winlongon register key...
1 | python vol.py -f zeus.vmem printkey -K "Microsoft\Windows NT\CurrentVersion\Winlogon" |
You can see sdra64.exe will run when the computer starts. If you search on Google you can see a lot of websites talking about this process... It seems to be a trojan....
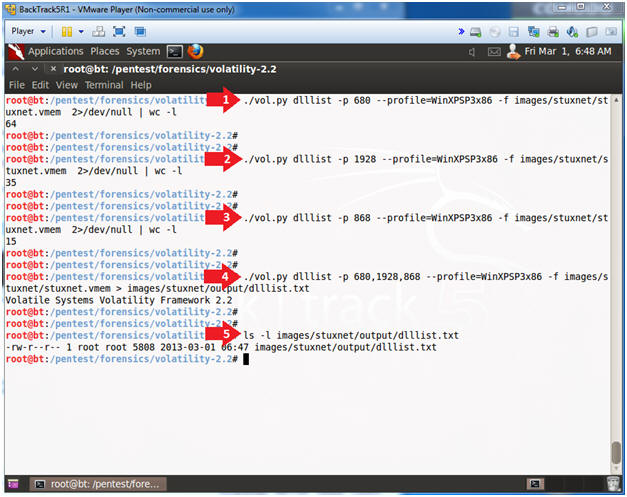
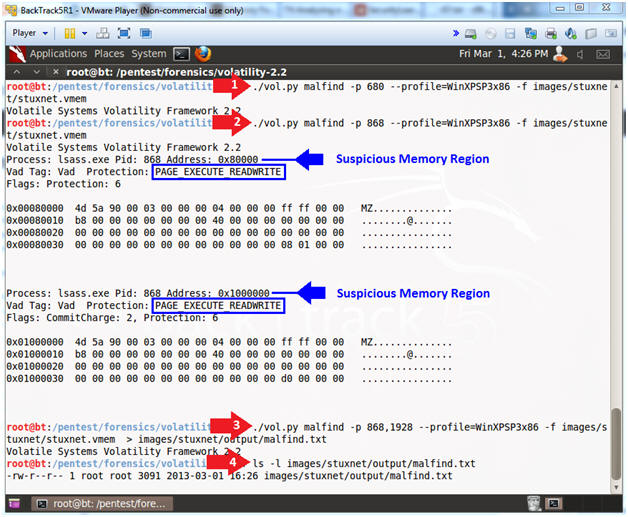
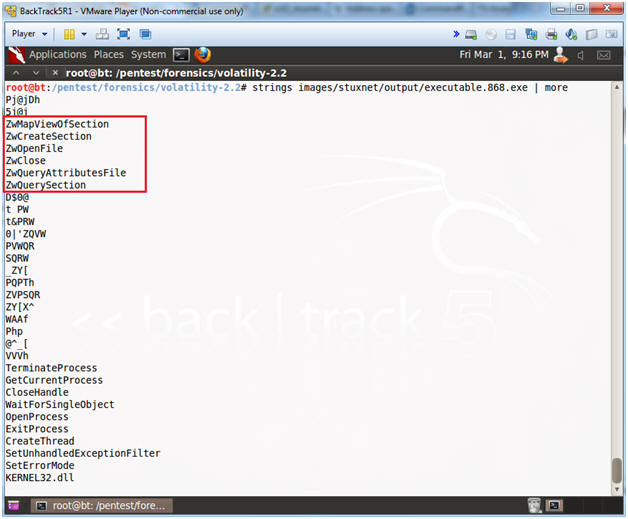
7) Now, we are going to try find a hidden or injected code/DLLs in the user mode memory and dump it...
1 | python vol.py -f zeus.vmem malfind --dump-dir evidencias/ |
9) Now, I'm going to get the SHA256 hash in order to search in Virustotal and see if this process is recognized by any Antivirus.
https://www.virustotal.com/en/file/8e3be5dc65aa35d68fd2aba1d3d9bf0f40d5118fe22eb2e6c97c8463bd1f1ba1/analysis/
Ok, so far so good.
10) We are going to use the mutantscan command. With this option, we can display all objects.
1 | python vol.py -f zeus.vmem mutantscan |
We noticed _AVIRA_2108... I don't know where I've heard this before...
1 | python vol.py -f zeus.vmem mutantscan | grep AVIRA |
I was looking for this object on Google. I visited www.fortiguard.com and found this.
11) This trojan usually shuts down our Firewall.. We can check it with the next command.
1 | python vol.py -f zeus.vmem printkey -K "ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile" |
This is evidence that the computer was infected with Zeus Trojan. In the next post, we are going to analyze another memory dump with Volatility.